Multifamily Made Easy
We deliver the most enjoyable leasing experience for renters and the most efficient tools for leasing teams.
Schedule a Demo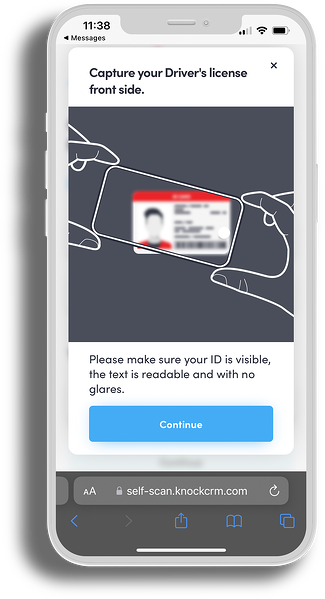






The most innovative, trusted, and fun platform in multifamily
With Knock, you can improve operational efficiency by profitably acquiring and retaining high-value, long-term residents, maximizing your NOI.
What We Do
Our integrated suite of front office technology provides multifamily owners and operators the levers they need to improve efficiency, maximize NOI, and effortlessly guide renters from lead to lease to retained resident.
Scheduling
With Knock Now™, prospective renters can self-schedule tours from any website or app, increasing tour volume 2.5x with no additional marketing expenses.
Attribution
With source attribution data, automated campaigns, and tools for every marketing channel, Knock® makes marketing easier (and smarter) than ever before.
Messaging
Communicate with high-quality leads across marketing channels — including email, text, voice, and chat — all through a single screen.
Task Management
Increase efficiency and drive NOI with a gamified leasing experience that prevents prospects from falling through the cracks and helps onsite teams hit their goals.
Visitor Experience
Create a modern renter experience by providing the most flexible conversion process in the industry.
Team Oversight
With benchmarking and performance trends that provide clear visibility into leasing team activity, leadership can give credit to high performers and provide additional support where needed.
Centralization
Empower leasing agents to work from anywhere, keep high-quality leads inside their company’s portfolio, and provide prospects more opportunities to lease — all from one dashboard.
Strategic Planning
Knock Insights has changed the way multifamily uses data, distilling billions of data points to help corporate teams and onsite managers gather quick insights, measure team performance, and budget with confidence.
Mobile Workforce
Knock Mobile ensures on-the-go leasing teams stay connected to their tasks, prospects, and property metrics, creating a fully mobile workforce that can close leads from anywhere.
What People Are Saying About Knock
Who is Knock for?

Leasing Teams
Delight your onsite teams with a fun and gamified leasing experience that drives leasing and renewals.

IT
Utilize our industry-leading partnership APIs and PMS integrations to adopt the technology your teams need, without creating new headaches for IT.
REPORT
Success in Multifamily Leasing Performance
Our survey of 700+ multifamily professionals reveals top operational priorities and areas of friction — and illuminates paths to align frontline and front office goals, improve performance, and drive success.

Resources
From case studies and e-books to research reports and templates, Knock® has the insights and resources multifamily teams need to succeed and grow.

The Value-Based Tech Buying Guide for Multifamily

Success in Multifamily Leasing Performance: Aligning Frontline and Front Office Priorities

See how Knockbot boosted Griffis Residential with a 45% increase in leads
- 8,800+ units
- 45% increase in leads
- 365% increase in converted leases










